how to protect rfid from rogue scanner One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from . In order to write to an NFC tag, an NFC reader/writer must first be connected. This then acts as an interface between the system and the NFC tag. In our example we use the NFC Reader/Writer DL533R from D-Logic. The .
0 · wireless rfid hacking
1 · rfid security problems
2 · rfid protection
3 · rfid hacking devices
4 · rfid card protection
5 · rfid card hacking
6 · how to prevent rfid hacking
7 · can rfid hackers work
The NFC reader is designed to function within a range of up to 15 millimeters .
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from . Lansweeper leverages patented device fingerprinting technology and advanced machine-learning techniques to identify and recognize all network-connected IT, OT, and IoT .
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from .
Lansweeper leverages patented device fingerprinting technology and advanced machine-learning techniques to identify and recognize all network-connected IT, OT, and IoT . RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently .
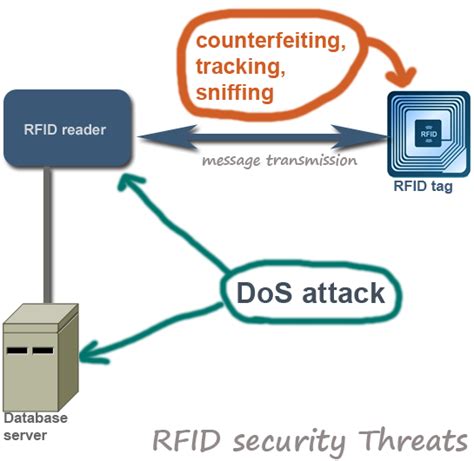
current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this .Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement .
wireless rfid hacking
First, you need to know how individuals outside of your organization could be accessing your RFID stored data illicitly. Two common methods of this are skimming and .
To stay safe from RFID hacking, there are several steps you can take. First, use RFID blocking wallets and bags to protect your credit and debit cards from unauthorized skimming. These .By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their .
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
RFID-blocking sleeves and wallets are commercially available and can protect RFID cards from unauthorized scans. These protective measures work by creating a Faraday cage .
rfid security problems
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from .
Lansweeper leverages patented device fingerprinting technology and advanced machine-learning techniques to identify and recognize all network-connected IT, OT, and IoT . RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently .
current RFID protocols are designed to optimize performance, with lesser attention paid to resilience and security. Consequently, most RFID systems are inherently insecure. In this .Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access. Enable Authentication: Implement .
First, you need to know how individuals outside of your organization could be accessing your RFID stored data illicitly. Two common methods of this are skimming and .To stay safe from RFID hacking, there are several steps you can take. First, use RFID blocking wallets and bags to protect your credit and debit cards from unauthorized skimming. These .
By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
rfid protection

360 carrier phase measurement for uhf rfid local positioning
bracelet rfid uhf
Near Field Communication (NFC) is a fast, intuitive technology that lets you interact securely .
how to protect rfid from rogue scanner|rfid security problems