rfid tag authentication In this paper, authentication for mobile radio frequency identification (RFID) systems with low-cost tags is studied. Firstly, an adaptive modulus (AM) encryption algorithm is proposed. Subsequently, in order to enhance the security without additional storage of new key matrices, a self-updating encryption order (SUEO) algorithm is designed. If you often work with NFC tags, NFC Reader Writer will make this process more efficient. With its simple interface and clear menu, the app is great for novice users. Learn all the features of NFC quickly and for free. You can .
0 · rfid tmis
1 · rfid tag authentication protocol
2 · rfid authentication tool
3 · rfid authentication protocol
4 · rfid authentication
5 · hid rfid support
6 · hid rfid authentication
7 · hid rfid
C has a formal grammar specified by the C standard. Line endings are generally not significant in C; however, line boundaries do have significance . See more
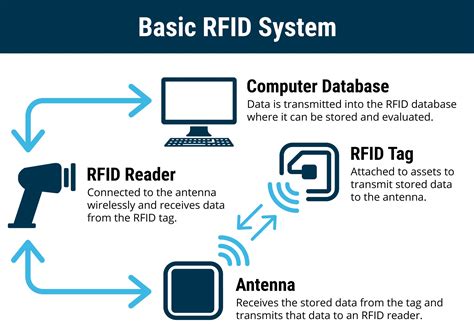
RFID-enabled identity authentication allows for an effortless, wireless exchange of information between devices. When RFID technology is embedded into a card, smartphone or wearable device, numerous use cases become possible.

public transit bus with smart card
In this paper, authentication for mobile radio frequency identification (RFID) systems with low-cost tags is studied. Firstly, an adaptive modulus (AM) encryption algorithm .RFID-enabled identity authentication allows for an effortless, wireless exchange of information between devices. When RFID technology is embedded into a card, smartphone or wearable device, numerous use cases become possible. In this paper, authentication for mobile radio frequency identification (RFID) systems with low-cost tags is studied. Firstly, an adaptive modulus (AM) encryption algorithm is proposed. Subsequently, in order to enhance the security without additional storage of new key matrices, a self-updating encryption order (SUEO) algorithm is designed.

rfid tmis
Gao and Lu [29] designed secure and efficient RFID tag-based authentication using bitwise XOR with the circular left-rotation operation. The model shows better results with low computational and communication costs.The Impinj Authenticity solution engine powers product authentication. With Impinj RAIN RFID-based product authentication, individual items are tagged with RAIN RFID tags featuring the Impinj M775 tag chip, each of which is programmed with a unique cryptographic key.
In this paper, we propose an RFID tag authentication based on frequency- and orientation-related phase fingerprints, called FopPrint, which does not require raw signal analysis or complex geometric relationship.A tamper-proof, near field communication (NFC) tag embedded into each product, combined with HID’s cloud-based authentication services, provide a unique and secure solution. And it’s fully compatible with NFC-enabled mobile phones, tablets and other similar devices. The robust authentication of RFID system components is critical in providing trustworthy data delivery from/to tags. In this paper, we propose an authentication protocol based on monitoring the transmissions between readers and tags in the system.In RFID authentication, every medication is given an RFID tag that uniquely identifies it. When a pharmacist needs to replenish the inventory, the RFID technology instantly helps them locate specific medications, like those in a recall situation.
rfid tag authentication protocol
rfid authentication tool
Commodity ultra-high-frequency (UHF) RFID authentication systems only provide weak user authentication, as RFID tags can be easily stolen, lost, or cloned by attackers. This paper presents the design and evaluation of SmartRFID, a novel UHF RFID authentication system to promote commodity crypto-less UHF RFID tags for security-sensitive .
ECPVS can be used sign an RFID tag and verify it using a reader with the corresponding public “verification” key. At the same time it can hide the Product Class ID from unauthorized readers without a verification key.
RFID-enabled identity authentication allows for an effortless, wireless exchange of information between devices. When RFID technology is embedded into a card, smartphone or wearable device, numerous use cases become possible.
In this paper, authentication for mobile radio frequency identification (RFID) systems with low-cost tags is studied. Firstly, an adaptive modulus (AM) encryption algorithm is proposed. Subsequently, in order to enhance the security without additional storage of new key matrices, a self-updating encryption order (SUEO) algorithm is designed. Gao and Lu [29] designed secure and efficient RFID tag-based authentication using bitwise XOR with the circular left-rotation operation. The model shows better results with low computational and communication costs.The Impinj Authenticity solution engine powers product authentication. With Impinj RAIN RFID-based product authentication, individual items are tagged with RAIN RFID tags featuring the Impinj M775 tag chip, each of which is programmed with a unique cryptographic key.In this paper, we propose an RFID tag authentication based on frequency- and orientation-related phase fingerprints, called FopPrint, which does not require raw signal analysis or complex geometric relationship.
A tamper-proof, near field communication (NFC) tag embedded into each product, combined with HID’s cloud-based authentication services, provide a unique and secure solution. And it’s fully compatible with NFC-enabled mobile phones, tablets and other similar devices. The robust authentication of RFID system components is critical in providing trustworthy data delivery from/to tags. In this paper, we propose an authentication protocol based on monitoring the transmissions between readers and tags in the system.
In RFID authentication, every medication is given an RFID tag that uniquely identifies it. When a pharmacist needs to replenish the inventory, the RFID technology instantly helps them locate specific medications, like those in a recall situation.Commodity ultra-high-frequency (UHF) RFID authentication systems only provide weak user authentication, as RFID tags can be easily stolen, lost, or cloned by attackers. This paper presents the design and evaluation of SmartRFID, a novel UHF RFID authentication system to promote commodity crypto-less UHF RFID tags for security-sensitive .
rfid authentication protocol
rfid authentication
Pull requests 3 - GitHub - nfcpy/nfcpy: A Python module to read/write NFC tags or .
rfid tag authentication|hid rfid support