guidelines for securing radio frequency identification rfid systems This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world . Check out our metal nfc business card selection for the very best in unique or custom, .
0 · what is an rfid system
1 · rfid radio frequency identification systems
2 · rfid radio frequency identification readers
3 · rfid is involved when using
4 · radio frequency tracking
5 · radio frequency identification rfid definition
6 · radio frequency identification rfid 1970s
7 · explain rfid in detail
Check if you're ready to make contactless payments. To tap to pay with Google Wallet: Near Field Communication (NFC) must be turned on. To make a pay contactless transaction with a card .
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .
It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks. The document also provides background information on RFID applications, standards, and system components to assist in the understanding of RFID security risks and controls. This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. Special Publication 800-series Karygiannis, A. , Eydt, B. , Barber, G. , Bunn, L. and Phillips, T. (2007), Guidelines for securing Radio Frequency Identification (RFID) systems:, , National Institute of Standards .
This bulletin provides an overview of RFID technologies and recommends practices for initiating, designing, implementing, and operating RFID systems in a manner that mitigates security and privacy risks.New Guidelines on RFID System Security The National Institute of Standards and Technology (NIST) Information Technology Laboratory recently published new guidelines on protecting RFID systems. NIST Special Publication (SP) 800-98, Guidelines for Securing RFID Systems: Recommendations of the National Institute of Standards andGuidelines for Securing Radio Frequency Identification (RFID) Systems: Recommendations of the National Institute of Standards and TechnologyDocument Citations. Citations available for content in Chicago, APA and MLA format. Citations are generated automatically from bibliographic data as a convenience and may not be complete or accurate.
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that .
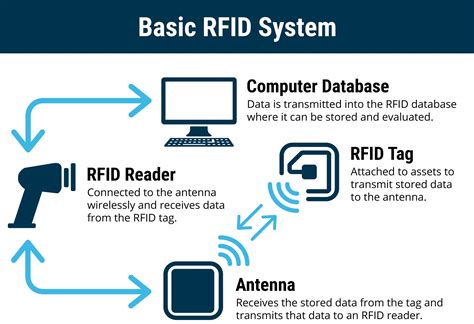
An RFID system for nuclear materials management consists of battery-powered RFID tags with onboard sensors and memories, a reader network, application software, a database server and web pages, and a miniature onboard dosimeter is being developed for applications that require radiation surveillance. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks. The document also provides background information on RFID applications, standards, and system components to assist in the understanding of RFID security risks and controls. This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks.
administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. Special Publication 800-series
Karygiannis, A. , Eydt, B. , Barber, G. , Bunn, L. and Phillips, T. (2007), Guidelines for securing Radio Frequency Identification (RFID) systems:, , National Institute of Standards . This bulletin provides an overview of RFID technologies and recommends practices for initiating, designing, implementing, and operating RFID systems in a manner that mitigates security and privacy risks.New Guidelines on RFID System Security The National Institute of Standards and Technology (NIST) Information Technology Laboratory recently published new guidelines on protecting RFID systems. NIST Special Publication (SP) 800-98, Guidelines for Securing RFID Systems: Recommendations of the National Institute of Standards andGuidelines for Securing Radio Frequency Identification (RFID) Systems: Recommendations of the National Institute of Standards and Technology
Document Citations. Citations available for content in Chicago, APA and MLA format. Citations are generated automatically from bibliographic data as a convenience and may not be complete or accurate.This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that .
is john lewis partnership card contactless

what is an rfid system
Android Smart Card Emulator. ¶. The Android Smart Card Emulator allows the emulation of a contact-less smart card. The emulator uses Android’s HCE to fetch APDUs from a contact-less .
guidelines for securing radio frequency identification rfid systems|radio frequency tracking