mifare classic card hack The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single . On Track Innovations Ltd. , a global provider of near field communication and .
0 · MIFARE ultralight vs classic
1 · MIFARE classic vs desfire
2 · MIFARE classic download
3 · MIFARE classic card recovery tool
4 · MIFARE classic card format
5 · MIFARE classic 1k cards
6 · MIFARE classic 1k card specification
7 · MIFARE 1k vs 4k
Homework. FM radio flowgraph: Create a flowgraph in GNU Radio Companion like the one in the video or the screenshot below. Test the flowgraph by listening to a strong FM radio signal. Add a channel slider: Add a slider to your FM .
Initial scans with NFC Tools revealed the card was an Infineon MIFARE Classic Card 1k. These cards are considered fairly old and insecure by now. There’s plenty of guides online on how to. The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single .The Mifare Cracking GUI (mcgui) identifies, cracks, and clones both original and hardened . MIFARE Classic ones especially, which are still widely used nowadays despite .
CRYPTO-1 uses two 48 bits-long keys on Mifare Classic cards to encrypt the data on its sectors. Each key can be configured to be used for reading or writing on a sector. On the Classic 1k,. New Design RFID-PN532: https://shop.mtoolstec.com0:00 Quick look on the . In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic . Mifare Classic in general is stated insecure, because it’s encryption protocol has been cracked. More deatiled Information about this can be found in the following links: .

– The use of Mifare Classic Cards for any system gives the fake sensation of security because it’s cracked since 2007 and exists public exploits since 2009 that allows anyone to clone/copy those cards as demonstrated. – The unique effective solution is exchange all cards in circulation by more secure cards. (Ex: Initial scans with NFC Tools revealed the card was an Infineon MIFARE Classic Card 1k. These cards are considered fairly old and insecure by now. There’s plenty of guides online on how to.How to Crack Mifare 1k RFID card. The NFC tag I analyzed is a so called “Mifare Classic 1k” tag. 1k stands for the size of data the tag can store. There are also other types like the “Mifare Classic 4k” and the “Mifare Mini” each having a different memory size. A Mifare Classic 1k tag contains 16 sectors. Each of these sectors has 3 . The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.
The Mifare Cracking GUI (mcgui) identifies, cracks, and clones both original and hardened Mifare Classic cards. Mcgui provides a simple user interface for existing Mifare cracking functions. The available cracking options through mcgui are the Dark Side, Hard Nested, and Nested attacks. MIFARE Classic ones especially, which are still widely used nowadays despite the many hacks found throughout the last few years. This is not intended to teach you all about RFID, NFC, and MIFARE hacking.
CRYPTO-1 uses two 48 bits-long keys on Mifare Classic cards to encrypt the data on its sectors. Each key can be configured to be used for reading or writing on a sector. On the Classic 1k,.New Design RFID-PN532: https://shop.mtoolstec.com0:00 Quick look on the phone and card for testing.0:30 Read original data with Mifare Classic Tool0:56 Read .In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic 1K cards using the Proxmark3 RDV4 and the RFID Tools Android App by RRG. Thi. Mifare Classic in general is stated insecure, because it’s encryption protocol has been cracked. More deatiled Information about this can be found in the following links: http://www.cs.ru.nl/~flaviog/publications/Attack.MIFARE.pdf. http://www.cs.ru.nl/~flaviog/publications/Dismantling.Mifare.pdf
– The use of Mifare Classic Cards for any system gives the fake sensation of security because it’s cracked since 2007 and exists public exploits since 2009 that allows anyone to clone/copy those cards as demonstrated. – The unique effective solution is exchange all cards in circulation by more secure cards. (Ex: Initial scans with NFC Tools revealed the card was an Infineon MIFARE Classic Card 1k. These cards are considered fairly old and insecure by now. There’s plenty of guides online on how to.How to Crack Mifare 1k RFID card. The NFC tag I analyzed is a so called “Mifare Classic 1k” tag. 1k stands for the size of data the tag can store. There are also other types like the “Mifare Classic 4k” and the “Mifare Mini” each having a different memory size. A Mifare Classic 1k tag contains 16 sectors. Each of these sectors has 3 .
The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.The Mifare Cracking GUI (mcgui) identifies, cracks, and clones both original and hardened Mifare Classic cards. Mcgui provides a simple user interface for existing Mifare cracking functions. The available cracking options through mcgui are the Dark Side, Hard Nested, and Nested attacks. MIFARE Classic ones especially, which are still widely used nowadays despite the many hacks found throughout the last few years. This is not intended to teach you all about RFID, NFC, and MIFARE hacking.
CRYPTO-1 uses two 48 bits-long keys on Mifare Classic cards to encrypt the data on its sectors. Each key can be configured to be used for reading or writing on a sector. On the Classic 1k,.New Design RFID-PN532: https://shop.mtoolstec.com0:00 Quick look on the phone and card for testing.0:30 Read original data with Mifare Classic Tool0:56 Read .In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic 1K cards using the Proxmark3 RDV4 and the RFID Tools Android App by RRG. Thi.
rfid tag reader pdf
MIFARE ultralight vs classic
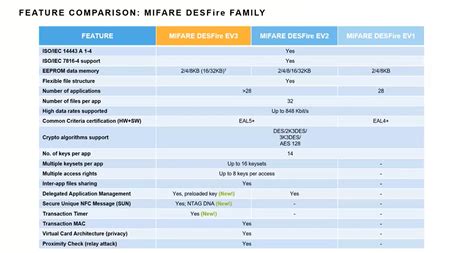
MIFARE classic vs desfire
MIFARE classic download
How can EMV data be read on Android via the NFC API? (Obviously, it's .
mifare classic card hack|MIFARE classic 1k card specification