smart card network security ppt How are Smart Cards Used? Information Technology Secure logon and authentication of users to PCs and networks Encryption of sensitive data Other Applications Over 4 million small dish TV .
Learn how to send and receive NFC data in the form of NDEF messages and how to handle NFC tags with the tag dispatch system. Find out how to parse NDEF records, map MIME types and URIs, and declare intent .
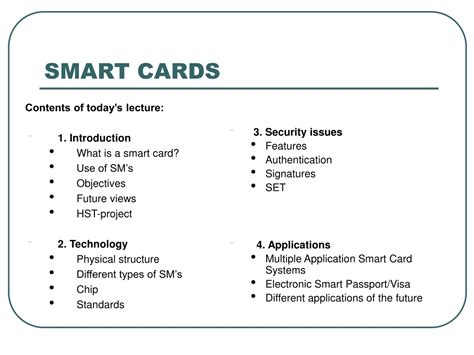
0 · Smart card ppt
1 · Smart card
2 · Smart Card Technology
3 · Smart Card Security
4 · Smart Card Digital Security Initiative
5 · PPT
6 · Introduction to Smartcard Security
7 · ECE4112 Smart Card Security
The easiest way is to use Passcreator to issue the passes for Google Wallet and a Socket Mobile S550 as the reader. I set it up for my independent gym and it's very fun to use :) . You need .
Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, .
rfid reader small
Smart cards improve security over other machine-readable cards by providing .The document outlines the history of smart cards from their invention in 1968 to . Smart cards improve security over other machine-readable cards by providing secure authentication, encryption, passwords, biometrics and more. Standards like ISO 7816 .
Smart cards offer security features like authentication, encryption, and secure data storage. They are used for applications like ID cards, payment systems, and building access .How are Smart Cards Used? Information Technology Secure logon and authentication of users to PCs and networks Encryption of sensitive data Other Applications Over 4 million small dish TV .ECE4112 Smart Card Security Nicholas Dorsey Steven Hurst April 28 2005
The smartcard is simply a card with an Integrated Circuit that could be programmed. This technology has been used widely in our daily lives and will become one of .
Goals Promote the critical role of smart card technology in securing B2B e-business, enterprise systems, bank card transactions, and consumer Internet applications; Help ensure the smooth .
Overview • Introduction • Security Technologies • Physical structure and life cycle • Communication with the outside world • Operating system • Attacks on Smart Card • Conclusion. Introduction • Smart card is a .
Smart card security Speaker: 陳 育 麟 Advisor: 陳 中 平 教授. Outline • Introduction of SCAs • Cryptographic Algorithms • Measurements • Hamming Weight • Simple Power . The document outlines the history of smart cards from their invention in 1968 to modern applications. Key benefits include security, portability and ease of use. Examples of smart card applications provided are banking, . Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, .
Smart cards improve security over other machine-readable cards by providing secure authentication, encryption, passwords, biometrics and more. Standards like ISO 7816 . Smart cards offer security features like authentication, encryption, and secure data storage. They are used for applications like ID cards, payment systems, and building access .
How are Smart Cards Used? Information Technology Secure logon and authentication of users to PCs and networks Encryption of sensitive data Other Applications Over 4 million small dish TV .ECE4112 Smart Card Security Nicholas Dorsey Steven Hurst April 28 2005 The smartcard is simply a card with an Integrated Circuit that could be programmed. This technology has been used widely in our daily lives and will become one of .Goals Promote the critical role of smart card technology in securing B2B e-business, enterprise systems, bank card transactions, and consumer Internet applications; Help ensure the smooth .
Overview • Introduction • Security Technologies • Physical structure and life cycle • Communication with the outside world • Operating system • Attacks on Smart Card • .
Smart card security Speaker: 陳 育 麟 Advisor: 陳 中 平 教授. Outline • Introduction of SCAs • Cryptographic Algorithms • Measurements • Hamming Weight • Simple Power .
Smart card ppt
The document outlines the history of smart cards from their invention in 1968 to modern applications. Key benefits include security, portability and ease of use. Examples of . Smart cards use microprocessors and memory to store and process encrypted data for transactions and access control through card readers. They provide flexibility, . Smart cards improve security over other machine-readable cards by providing secure authentication, encryption, passwords, biometrics and more. Standards like ISO 7816 .
Smart cards offer security features like authentication, encryption, and secure data storage. They are used for applications like ID cards, payment systems, and building access .How are Smart Cards Used? Information Technology Secure logon and authentication of users to PCs and networks Encryption of sensitive data Other Applications Over 4 million small dish TV .ECE4112 Smart Card Security Nicholas Dorsey Steven Hurst April 28 2005 The smartcard is simply a card with an Integrated Circuit that could be programmed. This technology has been used widely in our daily lives and will become one of .
Goals Promote the critical role of smart card technology in securing B2B e-business, enterprise systems, bank card transactions, and consumer Internet applications; Help ensure the smooth .
Overview • Introduction • Security Technologies • Physical structure and life cycle • Communication with the outside world • Operating system • Attacks on Smart Card • . Smart card security Speaker: 陳 育 麟 Advisor: 陳 中 平 教授. Outline • Introduction of SCAs • Cryptographic Algorithms • Measurements • Hamming Weight • Simple Power .
Smart card
Auburn Radio. Alabama. Ball State Baylor Baylor KSKY 660 AM. Texas. KMWX 92.5 FM. Texas. KZRK 107.9 FM. Texas. KTAE 1260 AM. Texas. KWBY 98.5 FM. Texas. KTON 1330 AM. .
smart card network security ppt|Smart card ppt