secure symmetric authentication for rfid tags ppt The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose . Icons licensed for merchandise. You can group your results by author style, pack, or see all available icons on your screen. Nfc Icons. 1,606 nfc icons. Vector icons in SVG, PSD, PNG, .
0 · Secure Symmetric Authentication for RFID Tags
1 · SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS
2 · Presentation On SECURE SYMMETRIC AUTHENTICATION
3 · ElProCus
$35.96
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose .Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø .In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is .Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for .
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.
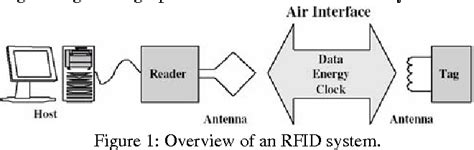
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
The document outlines security risks like spoofing, replay attacks, and unauthorized tracking. It emphasizes the need for lightweight cryptography and random number generation on tags to address security challenges in RFID systems. Read more. In this paper, we propose an RFID mutual authentication protocol employing ultra-lightweight mathematic primitives to achieve secure tag/reader authentication.This work employs a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID tag, and proposes an authentication mechanism to overcome current vulnerabilities. Expand
In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictableSilicon area is about 10,000 gates for such tags and cost about 50 cents. In this paper, we demonstrate how current RFID system is refined to introduce with the project ART (Authentication for long-range RFID systems) by providing secure authentication.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
The document outlines security risks like spoofing, replay attacks, and unauthorized tracking. It emphasizes the need for lightweight cryptography and random number generation on tags to address security challenges in RFID systems. Read more.
In this paper, we propose an RFID mutual authentication protocol employing ultra-lightweight mathematic primitives to achieve secure tag/reader authentication.This work employs a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID tag, and proposes an authentication mechanism to overcome current vulnerabilities. Expand
how to deactivate smart sim card via text
In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictable
Secure Symmetric Authentication for RFID Tags
how to change mobile no in smart ration card
how to check balance in bmtc smart card
how to consildate metro smart cards
how to close exxon mobil smart card
Playoff Flashback, Jan. 8, 2011: NFC wild card, Seattle 41, Saints 36 The Saints fell to the Seahawks 41-36 Jan 02, 2014 at 05:24 AM .
secure symmetric authentication for rfid tags ppt|Secure Symmetric Authentication for RFID Tags