conclusion of rfid based security system This paper briefly presents the current solutions to security and privacy of RFID . Over time, NFC tags may accumulate dirt, dust, or debris, which can hinder their functionality and impede successful communication with devices. If you encounter the .NFC (Near Field Communication) technology is a short-range, wireless technology that lets you quickly and wirelessly exchange information between your phone and other NFC-enabled .
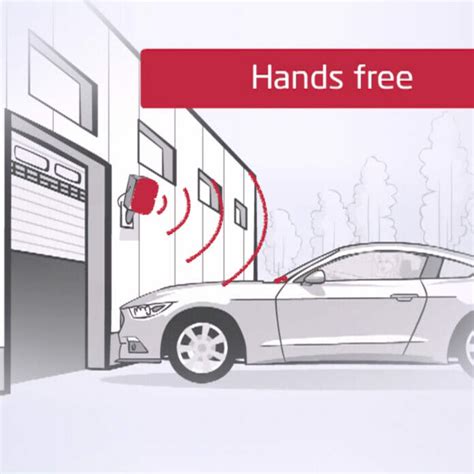
0 · rfid gate entry systems
1 · rfid gate access control systems
2 · rfid entry gate readers
3 · rfid door entry system
4 · rfid based door access control
5 · rfid access control system price
6 · door locking system using rfid
7 · best rfid for access control
no library for the simple usage of NXPs NFC reader exists so here you go - duinj/CLRC663_LPCD . no library for the simple usage of NXPs NFC reader exists so here you go - duinj/CLRC663_LPCD. Skip to content. Navigation .
rfid gate entry systems
As Sanjay Sarma states in presenting applications for RFID (Ch. 2), passive RFID technology is still in its infancy. We have identified challenging aspects of linking autonomous agents and intelligent handling systems (Ch. 14) with large volumes of distributed data sources . With the help of histogram of oriented gradients (HOG), face recognition . This paper briefly presents the current solutions to security and privacy of RFID .
Literature Review. RFID-Based Door Locking Systems: Several studies have explored the use .
As Sanjay Sarma states in presenting applications for RFID (Ch. 2), passive RFID technology is still in its infancy. We have identified challenging aspects of linking autonomous agents and intelligent handling systems (Ch. 14) with large volumes of distributed data sources such as RFID (Ch. 7).
With the help of histogram of oriented gradients (HOG), face recognition algorithm, RFID, and one-time passcode on registered email id, an intruder-free security system can be achieved. This paper briefly presents the current solutions to security and privacy of RFID application system. After that an improved approach is proposed which is based on random number assisting and.Literature Review. RFID-Based Door Locking Systems: Several studies have explored the use of RFID technology for access control in door locking systems. Research by Li et al. (2017) demonstrated the effectiveness of RFID-based authentication for securing access to buildings, showcasing its convenience and scalability.
Specifically in the defense and security section, we addressed how military and airports/ports manage RFID systems to ensure security. We also found that RFID is effectively implemented in prison management and child protection programs.
The RFIDbased access control with electromagnetic lock and intruder alert consists of three main parts-the INPUT (RFID), CONTROL (ATMega 328), and OUTPUT (Electromagnetic lock, LCD, Buzzer, and.1.1 Introduction to RFID security system. 1.2 Aim of the project. 1.3 Technical Approach. 1.4 Hardware Description.
However, RFID is transmitted wirelessly creating security risks that must be handled to prevent tag data from being corrupted and to prevent unauthorized access to both information and buildings.This work uses the possibility of improving access control door security by replacing a door key with a dependable electromagnetic door lock system for only authorized persons utilizing RFID and a mobile call intruder warning system.2. PROPOSED STRUCTURE AND DESIGN OF THE SYSTEM. In this study, we proposed a security system contains door locking system using passive type of rfid. The system is implemented in three spaces using central database system. As Sanjay Sarma states in presenting applications for RFID (Ch. 2), passive RFID technology is still in its infancy. We have identified challenging aspects of linking autonomous agents and intelligent handling systems (Ch. 14) with large volumes of distributed data sources such as RFID (Ch. 7).
With the help of histogram of oriented gradients (HOG), face recognition algorithm, RFID, and one-time passcode on registered email id, an intruder-free security system can be achieved. This paper briefly presents the current solutions to security and privacy of RFID application system. After that an improved approach is proposed which is based on random number assisting and.

rfid gate access control systems
Literature Review. RFID-Based Door Locking Systems: Several studies have explored the use of RFID technology for access control in door locking systems. Research by Li et al. (2017) demonstrated the effectiveness of RFID-based authentication for securing access to buildings, showcasing its convenience and scalability.Specifically in the defense and security section, we addressed how military and airports/ports manage RFID systems to ensure security. We also found that RFID is effectively implemented in prison management and child protection programs. The RFIDbased access control with electromagnetic lock and intruder alert consists of three main parts-the INPUT (RFID), CONTROL (ATMega 328), and OUTPUT (Electromagnetic lock, LCD, Buzzer, and.1.1 Introduction to RFID security system. 1.2 Aim of the project. 1.3 Technical Approach. 1.4 Hardware Description.
However, RFID is transmitted wirelessly creating security risks that must be handled to prevent tag data from being corrupted and to prevent unauthorized access to both information and buildings.
This work uses the possibility of improving access control door security by replacing a door key with a dependable electromagnetic door lock system for only authorized persons utilizing RFID and a mobile call intruder warning system.
38. Free. Get. Do you want to create your own NFC tags? NFC Kits is a App to read/write .
conclusion of rfid based security system|rfid gate entry systems