research paper on the security of rfid tags aniketh parmar This study examines the application and potential vulnerabilities of Radio Frequency . $18.00
0 · rfid transportation review
1 · rfid technology pdf
2 · rfid security review pdf
3 · rfid research paper
4 · rfid authentication review
5 · rfid applications and security review
6 · rfid applications and security pdf
For NFC payments to work, someone has to hold their mobile device or tap-to-pay card close to an NFC-enabled reader. The reader then uses NFC technology to search for and identify that payment device. Once it finds .
rfid transportation review
use of Radio-Frequency IDentiflcation (RFID) tags in shipping containers has been . This study examines the application and potential vulnerabilities of Radio .
This paper presents a review of the most cited topics regarding RFID focused on .
current nfc team standings
This study examines the application and potential vulnerabilities of Radio Frequency .Authors: Burkhard Englert, Parmar, Aniketh, Byambajav, Dolgorsuren, California Department of . In this paper, we review some of the recent research works using RFID solutions . This paper surveys recent technical research on the problems of privacy and .
This paper surveys recent technical research on the problems of privacy and . In this paper, we propose mechanisms that can achieve usable security and .
Security threats in RFID tags Information security researchers from Australia .use of Radio-Frequency IDentiflcation (RFID) tags in shipping containers has been suggested. RFID tags ideally can be used to identify and monitor individual contain-ers without physically having to inspect them. However these tags themselves can possible become security risks. In this research project we studied the potential vul-
This study examines the application and potential vulnerabilities of Radio Frequency Identification (RFID) tags in shipping containers. While RFID tags can easily be used for identifying and monitoring individual containers without their physical inspection, the tags can still pose security risks. This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. A total of 62,685 records were downloaded from the of Science (WoS).This study examines the application and potential vulnerabilities of Radio Frequency Identification (RFID) tags in shipping containers. While RFID tags can easily be used for identifying and monitoring individual containers without their physical .Authors: Burkhard Englert, Parmar, Aniketh, Byambajav, Dolgorsuren, California Department of Transportation, California State University, Long Beach Department of Computer Engineering and Computer Science, Metrans Transportation Center, .
In this paper, we review some of the recent research works using RFID solutions and dealing with security and privacy issues, we define our specific parameters and requirements allowing us. This paper surveys recent technical research on the problems of privacy and security for radio frequency identification (RFID). RFID tags are small, wireless devices that help identify objects and people.
This paper surveys recent technical research on the problems of privacy and security for radio frequency identification (RFID). RFID tags are small, wireless devices that help identify.
In this paper, we propose mechanisms that can achieve usable security and privacy in an RFID system. First, we discuss the application of security and privacy policies to provide both fine-grain access control to the tags' information, stored in a .
Security threats in RFID tags Information security researchers from Australia published a paper describing a method to prevent a reader from reading information from an RFID tag. The method based on the principle of DDoS attacks was used in the work: the radio air is filled with a huge number of signals simulating the signals of RFID tags.use of Radio-Frequency IDentiflcation (RFID) tags in shipping containers has been suggested. RFID tags ideally can be used to identify and monitor individual contain-ers without physically having to inspect them. However these tags themselves can possible become security risks. In this research project we studied the potential vul- This study examines the application and potential vulnerabilities of Radio Frequency Identification (RFID) tags in shipping containers. While RFID tags can easily be used for identifying and monitoring individual containers without their physical inspection, the tags can still pose security risks. This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. A total of 62,685 records were downloaded from the of Science (WoS).
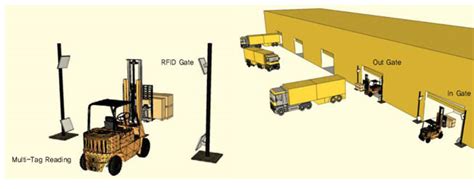
This study examines the application and potential vulnerabilities of Radio Frequency Identification (RFID) tags in shipping containers. While RFID tags can easily be used for identifying and monitoring individual containers without their physical .Authors: Burkhard Englert, Parmar, Aniketh, Byambajav, Dolgorsuren, California Department of Transportation, California State University, Long Beach Department of Computer Engineering and Computer Science, Metrans Transportation Center, . In this paper, we review some of the recent research works using RFID solutions and dealing with security and privacy issues, we define our specific parameters and requirements allowing us.
This paper surveys recent technical research on the problems of privacy and security for radio frequency identification (RFID). RFID tags are small, wireless devices that help identify objects and people. This paper surveys recent technical research on the problems of privacy and security for radio frequency identification (RFID). RFID tags are small, wireless devices that help identify.
In this paper, we propose mechanisms that can achieve usable security and privacy in an RFID system. First, we discuss the application of security and privacy policies to provide both fine-grain access control to the tags' information, stored in a .
current nfc and afc standings
Discover one of Citi's best cash back rewards cards designed exclusively for .Apply by Phone: 1-800-259-3052. TTY: Use 711 or other Relay Service. Apply for Costco .
research paper on the security of rfid tags aniketh parmar|rfid transportation review