rfid based security system pdf Besides being vulnerable to common attacks such as eavesdropping, man-in-the-middle, and denial of service, RFID technology is, in particular, susceptible to spoofing and power attacks . Shop the T Mobile Sim Card 4g 5g with features, pricing and reviews. Pair it with one of our .
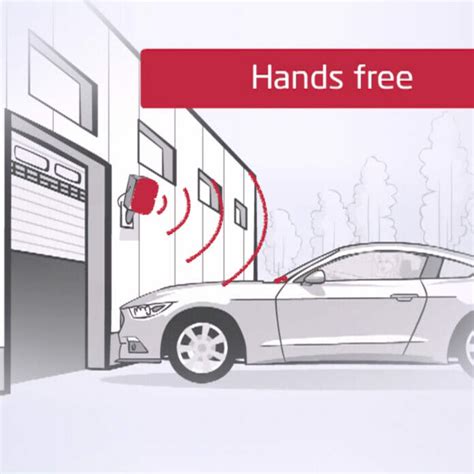
0 · rfid gate entry systems
1 · rfid gate access control systems
2 · rfid entry gate readers
3 · rfid door entry system
4 · rfid based door access control
5 · rfid access control system price
6 · door locking system using rfid
7 · best rfid for access control
Fix the unregistered SIM card issue. Here are 4 frequent methods of fixing the SIM .
Besides being vulnerable to common attacks such as eavesdropping, man-in-the-middle, and denial of service, RFID technology is, in particular, susceptible to spoofing and power attacks . With the help of histogram of oriented gradients (HOG), face recognition algorithm, RFID, and one-time passcode on registered email id, an intruder-free security system can be .Besides being vulnerable to common attacks such as eavesdropping, man-in-the-middle, and denial of service, RFID technology is, in particular, susceptible to spoofing and power attacks . With the help of histogram of oriented gradients (HOG), face recognition algorithm, RFID, and one-time passcode on registered email id, an intruder-free security system can be .
This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. A total of 62,685 records were downloaded from the of .However, RFID is transmitted wirelessly creating security risks that must be handled to prevent tag data from being corrupted and to prevent unauthorized access to both information and .
Here in this paper, endeavouring to repeat the thorough writing study identified with the different entryway bolts and gate security frameworks that are vital in the fields, for example, home, . Radio frequency identification (RFID) is widely used in several contexts, such as logistics, supply chains, asset tracking, and health, among others, therefore drawing the .

lg g7 nfc tag read
The RFIDbased access control with electromagnetic lock and intruder alert consists of three main parts-the INPUT (RFID), CONTROL (ATMega 328), and OUTPUT . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .. Abstract—This paper describes the design of RFID based security and access control system for use in hostels inside the Punjab University premises. The system combines RFID technology . RFID BASED AUTOMATED GATE SECURITY SYSTEM. Paper relies upon security access and control system using RFID and Arduino with GSM module, which is .
Besides being vulnerable to common attacks such as eavesdropping, man-in-the-middle, and denial of service, RFID technology is, in particular, susceptible to spoofing and power attacks . With the help of histogram of oriented gradients (HOG), face recognition algorithm, RFID, and one-time passcode on registered email id, an intruder-free security system can be . This paper presents a review of the most cited topics regarding RFID focused on applications, security, and privacy. A total of 62,685 records were downloaded from the of .However, RFID is transmitted wirelessly creating security risks that must be handled to prevent tag data from being corrupted and to prevent unauthorized access to both information and .
Here in this paper, endeavouring to repeat the thorough writing study identified with the different entryway bolts and gate security frameworks that are vital in the fields, for example, home, .
Radio frequency identification (RFID) is widely used in several contexts, such as logistics, supply chains, asset tracking, and health, among others, therefore drawing the .
The RFIDbased access control with electromagnetic lock and intruder alert consists of three main parts-the INPUT (RFID), CONTROL (ATMega 328), and OUTPUT . This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world .. Abstract—This paper describes the design of RFID based security and access control system for use in hostels inside the Punjab University premises. The system combines RFID technology .
rfid gate entry systems
For example, with the NTAG210µ chip, the total memory is 64 bytes. Of this, the 'usable memory' - the part you can put your data into - is 48 bytes. To store a web address, you will also need to store 8 bytes of 'hidden' .
rfid based security system pdf|rfid gate entry systems