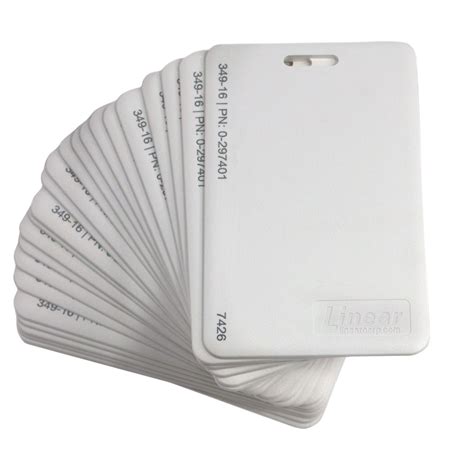
proximity id card and rfid blocking Shield Your Prox Card: Use RFID-blocking sleeves or wallets that prevent unwanted scanning of your card. These inexpensive solutions can stop would-be attackers from intercepting your card's signal. Card emulation with a secure element. When NFC card emulation is provided using a secure element, the card to be emulated is provisioned into the secure element on the device through an Android application. Then, when .
0 · what is hid proximity card
1 · hid proximity card types
2 · hid proximity access cards
3 · hid printable proximity cards
4 · hid 0009p proximity cards
5 · difference between rfid and proximity card
6 · difference between rfid and prox
7 · 125 khz proximity cards
Get in touch with Square's sales team to discuss your needs and find the right .

An industry has sprung up to make wallets and accessories that block hackers from "skimming" . There are even RFID-blocking wallets. One of the more drastic solutions we’ve found is to extract the RFID coil and chip from the card and just mount it into your smartphone – that way you can store your RFID transit card in your smartphone. An industry has sprung up to make wallets and accessories that block hackers from "skimming" data wirelessly through radio frequency identification. But some experts say there's little need to. Shield Your Prox Card: Use RFID-blocking sleeves or wallets that prevent unwanted scanning of your card. These inexpensive solutions can stop would-be attackers from intercepting your card's signal.
In this simple guide, we breakdown the differences between RFID cards vs proximity cards, including; when to use each one and the key differences. What I'm using it to test out here are Vulkit RFID blocking cards, which are designed to protect credit cards, debit cards, and ID cards using 13.56MHz-frequency RFID from unauthorized. RFID-blocking wallets are supposed to prevent your RFID card information from being stolen. But do they really work? Even then, is the danger real enough to make a purchase worth it? The simplest definition of proximity cards is as follows: They are access control cards that use RFID technology to communicate with card readers and grant access to secure areas or buildings. How do proximity cards work? Proximity cards operate using passive (no battery) technology.
A static magnetic field caused by a normal magnet should not cause any harm to a RFID-tag. Its all about speed of the movement of the RFID-Tag relative to the magnetic field. The antenna (a coil) of the RFID chip and the magnet form a generator. RFID blocking refers to the use of specialized products or materials that aim to prevent the unauthorized reading of RFID-enabled cards, passports, and other items. In this article, we will explore the concept of RFID blocking, how it works, and its benefits and limitations.
what is hid proximity card
What is RFID blocking? RFID readers can read information contained on wireless devices (tags) without physical contact. Furthermore, there doesn’t even need to be a line of sight for this to be achieved (although it does require close proximity). However, RFID blocking involves cutting off the electromagnetic signal emitted from a transceiver . There are even RFID-blocking wallets. One of the more drastic solutions we’ve found is to extract the RFID coil and chip from the card and just mount it into your smartphone – that way you can store your RFID transit card in your smartphone. An industry has sprung up to make wallets and accessories that block hackers from "skimming" data wirelessly through radio frequency identification. But some experts say there's little need to. Shield Your Prox Card: Use RFID-blocking sleeves or wallets that prevent unwanted scanning of your card. These inexpensive solutions can stop would-be attackers from intercepting your card's signal.
In this simple guide, we breakdown the differences between RFID cards vs proximity cards, including; when to use each one and the key differences. What I'm using it to test out here are Vulkit RFID blocking cards, which are designed to protect credit cards, debit cards, and ID cards using 13.56MHz-frequency RFID from unauthorized.
RFID-blocking wallets are supposed to prevent your RFID card information from being stolen. But do they really work? Even then, is the danger real enough to make a purchase worth it? The simplest definition of proximity cards is as follows: They are access control cards that use RFID technology to communicate with card readers and grant access to secure areas or buildings. How do proximity cards work? Proximity cards operate using passive (no battery) technology.A static magnetic field caused by a normal magnet should not cause any harm to a RFID-tag. Its all about speed of the movement of the RFID-Tag relative to the magnetic field. The antenna (a coil) of the RFID chip and the magnet form a generator.
RFID blocking refers to the use of specialized products or materials that aim to prevent the unauthorized reading of RFID-enabled cards, passports, and other items. In this article, we will explore the concept of RFID blocking, how it works, and its benefits and limitations.
hid proximity card types
hid proximity access cards
hid printable proximity cards
To program NFC tags, you’ll need an open NFC tag, an NFC-compatible smartphone, and an app to program the tags. Begin by launching the app, creating a task, and writing on the tag. You’ll be able to include other features like tag protection and tracking abilities.
proximity id card and rfid blocking|what is hid proximity card